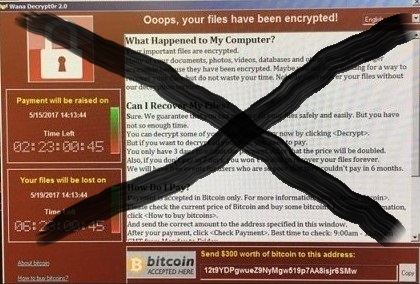
WannaCrypt Virus Epidemic Stopped by Abracadabra
The security expert @MalwareTechBlog stopped the WannaCrypt virus epidemy simply by registering a non-readable domain name. He confessed, “…I was unaware registering the domain would stop the malware until after I registered it, so initially it was accidental”.
The expert discovered a very curious line while looking at the virus code, which stated that once a specific domain was registered and owned, the virus would be ordered to quit. The creaters of the virus never actually expected anyone to actually register the domain, since the name required was: iuqerfsodp9ifjaposdfjhgosurijfaewrwergwea.com. Obviously, they just typed a slew of letters at random. But our hero did just that to see what would happen – he registered the domain and got thousands of requests from infested computers within minutes. Then, just like that, the virus stopped spreading from the infested machines!
Hackers must have been very smug about their resourcefulness when creating the virus. You see, any program has a basic command that it must continue doing it’s task until an assigned task is complete. It’s called the condition command or if-then command. This command sets the conditions of some action. For instance, let’s say you have to take all the toy bricks from one box and put them into another. What do you do? You look into the box #1 to see if there are any brick left. If you see any bricks remaining in the first box, you will pick them up and put it into the box #2. Once box #1 is empty, then there is no more work to be done and you are finished with your task. This is how a computer or virus works as well, it just looks like this: if brick > 1, then relocate it to the box #2, if brick = 0, then stop the task.
WannaCrypt wrote their virus to continue its task of infecting hardware until a certain domain had been registered. It’s clear that the writers didn’t actually expect anyone to ever actually register an incomprehensible domain name. And then, oops! The domain iuqerfsodp9ifjaposdfjhgosurijfaewrwergwea.com came into existence, and the virus did what it was programmed to do; it stopped.
MalwareTechBlog stopped the epidemic by studying the virus’ behavior and setting up a target sinkhole.
It didn’t take hours of typing in front of black displays with myriads of green lines running. Until the domain is revoked, the WannaCrypt is completely harmless! That’s what I call Bruce Willis style of rescuing the world.
There has been an animated world map developed to show people the scale of the cyber attack. Wannacry Ransomware Map shows data which was collected via one of the infested domains the blog took control of. The attack began at one and the same time around the globe and Europe seems to suffer most. The USA is relatively okay, but we’ll see, since the info is still being updated.
What can you do to stay safe in the future? First, remember to update all the patches and updates Microsoft provides. Second, remember to update your antivirus software. Third, regularly back up critical files to the hard drives or other computer with NO internet access.
- If you are tired of battling against all the dangers of Internet, you can easily trade in your computers and smartphones for top cash: Sell used electronics online today!
Man Who Stopped WannaCry Outbreak Arrested in USA
Text updated on August 8, 2017
In May the world was shaken by the outburst of the cruelest ransomware WannaCry. And the name of the malware was well to the point as it made cry people across the world. This was the first time the public facilities were injured and suffered malfunction.
The WannaCry’s march was stopped dead by a digital security expert under the alias of @MalwareTechBlog. He just registered the domain name the virus addressed to and this was the kill switch of it. Now you must know that the expert’s name is actually Marcus Hutchins, 22. He is a British national and on Wednesday he was arrested by US Marshals at Las Vegas airport. A Justice Department spokesperson has confirmed it on the phone.
Mr. Hutchins came to our country to attend the Def Con conference in Las Vegas. The indictment was dated July 11, two weeks previously. “The charges against Hutchins, and for which he was arrested, relate to alleged conduct that occurred between in or around July 2014 and July 2015,” said the spokesperson.
The indictment has to do not with the WannaCry ransomware but with the Kronos malware. The Kronos can steal credentials, legitimate banking websites and evade antivirus detection and sandbox environments. It can be built in every browser since it uses the vulnerabilities in them. Mr. Hutchins and another still anonymous defendant are accused of selling the malware on the dark-web marketplace AlphaBay.
The marketplace is now defunct and its founder and operator Alexandre Cazes – dead.
Such are the facts. And here we enter the morals grey zone. Like the one that existed long time ago in the Wild West, when gunfighters swapped sides every week and were now bandits and now sheriffs and the ways of both were hard to tell from one another. Surely, one doesn’t start an expert’s career in the digital security without any experience at all. But on what side of the law the experience is gained is another question. Should we turn a blind eye to the past of Mr. Hutchins and other ex-hackers now security experts or should we crack down on web criminals no matter what?





Facebook
Twitter
RSS