
Don’t buy a Portable WiFi Hotspot until you see this! [Video]
Video uploaded by Techs You Can’t Live Without on November 4, 2021
Security Once More or How to Make Your Hotspot Much Cooler in Terms of Safety
As we all know full well by now, there is a flipside to practically all good things (even Apple devices have their… yes, price). And the same goes for the fact that connectivity has become all but omnipresent these days. Yes, being able to go online pretty much everywhere is, on the whole a good thing (sometimes it might turn out even literally vital). But this convenience does come with certain security risks. Because it is provided to us by the public Internet access points known as hotspots.
And the key word here is “public”. Meaning – you guessed it, of course – that once you connect to the World Wide Web from there, your phone or your (often much less protected) laptop becomes dangerously open to the public as well. In other words, it gives more chances of accessing your data – from personal to work-related – to God knows who (yes, not-so-dear scammers and stalkers, we are looking at you). Be that the inbox checking or choosing a Christmas present on the go, the danger of stealing your essential info, down to your very identity is never far away. It starts lurking about whenever you hit that “connect” button.
But thankfully, the “ways and means” law works not just in favour of thieves and fraudsters. We can do something (actually, quite a few somethings) to use these access points with much more peace of mind than if we would just have dived into it unthinkingly. And of course, we are happy to share with you the most useful of the said somethings.
Look for the opt-in step in the process of connection (if there isn’t one, it’s probably a hacker who is masquerading as an official free hotspot).
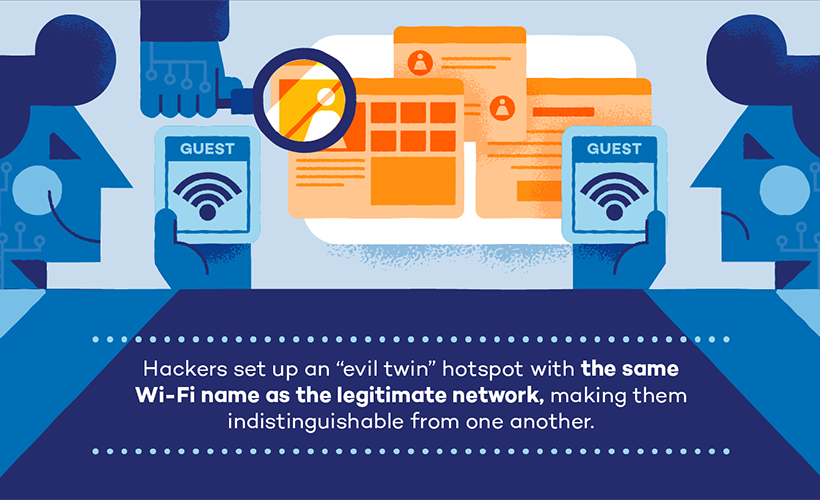
Of which precautions the first and foremost is, in our opinion, not taking the name of the network appearing in your wi-fi connections list for granted. Check it. Check it always, no matter how legitimate and safe it might appear. Ask the staff. Look for the opt-in step in the process of connection (if there isn’t one, it’s probably a hacker who is masquerading as an official free hotspot). Run the name of the connection against a trusted database if you can. But never go into it mindlessly, never assume. Like we said above, it’s not just the law-abiding public who have a lot more options and possibilities in our days.
Also, do everything in your power not to reveal your most sensitive info. Have your backup email address ready when asked for such data. Come up with a new password instead of just puttin in the one you use regularly. And, unless you are buying something urgently, never at all disclose anything related to your bank account (and no, the “s” at the end of the “http” part of address doesn’t guarantee much).
Another key point is not forgetting to forget, if you pardon us the pun. It’s not advisable to let your device “remember” any third-party connection, because in that case your phone or computer will consider it safe by default… and will connect to it all by itself whenever you’ll come into the area again, without letting you verify if this particular network is still OK to use. (Which it might not be by then). So always click “forget the network” once you no longer need this particular hotspot. And don’t worry, your device will still see it if need be.

Then there is one real winner for those wanting to be sure: the good old VPN. It pretty much covers all your bases, blocking both the data you use online and even your IP info from the view of any potential wrongdoer.
Then there is one real winner for those wanting to be sure: the good old VPN. It pretty much covers all your bases, blocking both the data you use online and even your IP info from the view of any potential wrongdoer. This would be the perfect option, almost rendering the rest of them redundant… but for one little detail. That is, with the virtual private network, if you want to be really sure, it is preferable to go for a paid product (or a premium version of the free ones). Because otherwise, you’ll never know how well you’ll be protected: a free lunch is a flawed lunch and all that.
And finally, especially if you don’t need to connect to a hotspot for too long a time, you can just go and create one yourself… out of your own mobile phone (the process also known as tethering). If you are an Android owner, you’ll find this function (which can be named variously, from “Mobile Network Sharing” to just plain “Tethering” itself; in other cases, there should be the “hotspot” in there somewhere) under the “Networks” (or “Connections”) section of the “Settings” menu. If you have an iPhone, select the “Personal hotspot” or “Mobile data” in your settings, or, if there is nothing of the sort there, go for “General”, click on “Network”, and there your “Personal Hotspot” will be). After that, all you will have to do is pick the “Wi-Fi” (or “Mobile hotspot”) connection, give it a name and create a not-too-easy password. Mind you, the latter is not compulsory, but leaving it for all and sundry to connect to (and use your own mobile data at that) kind of defies the purpose, does it not? (But we wouldn’t recommend this particular way of protection if your phone isn’t 5G-equipped, otherwise the speed of your connection and amount of data you spend in the process may well disappoint you).
So, as you see, with some precautions you can, after all, have all the perks without paying too heavy (and unfair, for that matter) price.
Links
- Improve mobile hotspot security in 5 steps – TechTarget
- Sell your used electronic device online – iGotOffer





Facebook
Twitter
RSS