
KeySteal – Stealing your keychain passwords on macOS Mojave [Video]
Video uploaded by Linus Henze on February 3, 2019
macOS Mojave Bug: Breaking News – Keychain is Vulnerable
An exploit is a software that literally “exploits” various vulnerabilities found in a computer’s system. When Apple Mac security specialist Patrick Wardle tested an exploit by Linus Henze, an 18-year-old German bug researcher, Wardle said, “Until Apple wraps its head around security, I’m shutting off my Mac and going surfing.” What did Henze find that alarmed the experienced security expert?
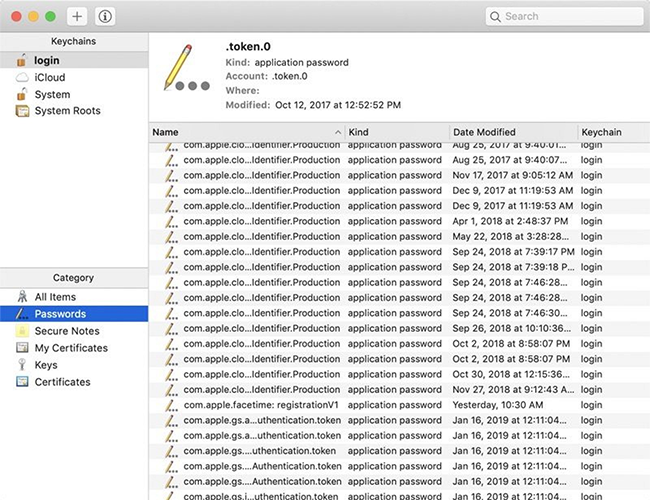
He found a great vulnerability in the most praised macOS Mojave security application, Apple Keychain. If you’re a Mac user, you surely save all your passwords in Keychain. It works as any password manager: you must enter your master password to gain access to the database. You can see in this video how easily Henze extracted the complete list of passwords.
He didn’t need root privileges to pull off the trick. Nor did System Integrity Protection prevent the hack! SIP was developed to protect registry changes like code injection, debugging, or tracing. SIP also prohibits unsigned kernel extensions and guards file integrity. It operates at a kernel level; once activated, it can disobey even root privileges. Ideally, all you have to do is flag the directory you want to protect and let SIP do its job. And yet—and yet!—the new bug is “invisible” to SIP. This means that the vulnerability is hidden in the kernel of the macOS Mojave. That it’s inseparable from its code. And that there’s no remedy against it.
Now I think you can better understand Wardle’s words. He was joking, of course, but not quite. I’ll tell you something that will make your hair stand on end: The Apple bug bounty program DOES NOT include macOS. In other words, researchers share their findings by their own volition. Henze doesn’t want to help Apple out of charity. He said to Forbes that finding vulnerabilities like that one took time, and he had every right to a reward. As none was offered, Henze chose to upload a short demo to inform the world. This YouTube video was viewed 11,000 times, but Apple is silent.
This is the other part of the problem: Apple is cosplaying an Egyptian sphinx. No one stepped forward and verbalized the company’s concerns over the issue. We have to cope with it on our own. What can we do to save our passwords? And do we have to do anything at all? Henze didn’t share his exploit; he’s a white hat hacker. However, there’s a chance that someone somewhere can reconstruct his algorithm. So, let’s follow the ‘better safe than sorry’ saying until Apple rolls out a patch.
Some websites advise adding additional master passwords to Keychain. I personally don’t see any use in it. A kernel bug doesn’t care how many passwords you add. The best way is to retrieve the passwords from Keychain and save them elsewhere. Here’s the list of options:
Copy your passwords to a text file and save the file on an unconnected device or other PC under an inconspicuous name.
Transfer the passwords to a reliable third-party password manager.
Take your time and create master password with at least 15 symbols.
Links
- Security researcher demos macOS exploit to access Keychain passwords, but won’t share details with Apple out of protest – 9to5Mac
- How to avoid further problems with MacOS Mojave Bug: Trade in your old Macbook for top dollar! – iGotOffer




Facebook
Twitter
RSS