
Apple Password Retry Limitations Cracked
Cambridge Professor Cracked Apple Password Retry Limitations
The FBI and Apple clash over unlocking the iPhone 5c belonging to the San-Bernardino shooter made headlines earlier this year. Apple refused to unlock the phone, while the FBI declared it was impossible. However, Professor Sergei Skorobogatov of Cambridge, graduate of MIFI in Moscow, Russia, brilliantly solved the problem. Surprisingly, it took him only $100 worth of equipment, most of it, including iPhone 5c spare parts, he bought on eBay.
So, we strongly recommend you to revise your iPhone passcode now, in the light of Professor Skorobogatov’s discovery.
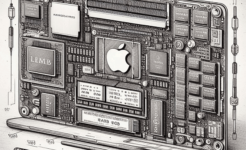
With that he managed to clone the NAND memory that houses the attempt retry counter, thus making the number of attempts limitless. According to his words, “a full scan of all possible 4-digit passcodes will take about 40 hours, or less than two days.” That would be enough in most cases, as many owners of hand held devices use 4-digit passcodes, such as dates of their birthdays or years of purchase. So, we strongly recommend you to revise your iPhone passcode now, in light of Professor Skorobogatov’s discovery.
It was a challenging task to fulfill, not one you can repeat at home unless you have the same expertise in the field.
As iPhone users know, you have just 10 attempts when entering the passcode. After 5 consecutive wrong entries a short waiting time of 5 seconds is added. The waiting time will increase with every next mistake, reaching up to 60 minutes before all the data is erased, leaving you unable to recover it. The UID key to calculate the passcode is the part of CPU firmware, and can’t be hacked Hollywood style with just a computer and a keyboard.
The most important task in this process is to back up the data so that it cannot be lost when entering wrong passcodes. The professor disassembled the iPhone 5c and cloned the NAND memory used for storage. This was a tricky process, because, first, the parts were not only soldered, but also glued with a strong epoxy compound.
Second, simply cloning the NAND memory won’t work with the iPhone 5C. iTunes refused to restore the phone and reported unknown errors 14 and 4013.
Part of the problem was the nature of NAND memory itself. NAND memory has cells to write the data in. Additional cells are allocated for error correction data. Faulty blocks are marked as unusable or replaced with a fresh one. Apple uses Perfect Page New (PPN) technology for this.
While being cloned, the data is rearranged and written in other cells. Now, Apple CPU firmware can’t ‘find’ it in the proper places. It’s like arranging items in your desk drawers or garage shelves. You got used to placing, say, your drill on a shelf by the door, and now it’s on the floor in a box. Or your pencil sharpener has moved from the top drawer to the bottom. A bit irritating, isn’t it?
Another issue is that NAND memory can sustain only a limited number of writing cycles. So, you’ll have to get not one, but several NAND clones to replace them while trying a passcode.
For more elaborate technical details, we invite our readers to click the footnote.
With the issues with NAND memory cloning solved, the procedure of hacking the retry counter is as follows: first, you will need a test board, plugged into a PC with logic analyzer, a number of cloned NAND modules, and a disassembled iPhone. Plug the clones in turn into the disassembled iPhone, power it up, and attempt to enter a passcode. After 6 wrong entries you power the smartphone down, wait about 10 seconds for the power to be taken from NAND, swap the NAND clone, and then repeat.
Here’s the video, posted by Sergei Skorobogatov to illustrate the whole process:
The experts see absolutely no problems with applying this technology to iPhone 6 and iPhone 7 hacking. What does this mean for us, end-users? First, as we have mentioned above, reconsider your passcode length. It must be at least 8-digits long. Second, try not to leave your iPhone unattended. If you lost your iPhone or it was stolen from you, follow the Apple guide. If you fear that your password isn’t hack proof enough, erase the phone remotely. In this case, don’t forget to back up the data on your smartphone regularly. Remember to also call your wireless carrier and ask them to block your account.
See also:
- Source: igotoffer.com/apple/bumpy-road-success/
- Apple Encyclopedia: all information about company, products, electronic devices, operating systems and apps from iGotOffer experts.
- Switching to a new device? Trade in your old gadget for fast cash at iGotOffer.com. We pay the best price online for the secondhand Apple devices and any other electronic device for this matter. Free instant quote, free fully insured shipping, fast and secure payment.



Facebook
Twitter
RSS